Description
The security vulnerability associated with USB based attacks continues to exist and presents a real danger to billions of computer users in the world as Hardware Trojan Horse Devices can automatically breach a computer system. The research community has not fully understood the security risk related to USB. USB protocol of poorly regulated device self-identification provides the opportunity for Hardware Trojan Horse Device to represent itself as a Human Interface Device.
The importance of this study is the construction and execution of Hardware Trojan Horse Mouse attacks that is connected to a USB end point of a personal computer. The work presented the scenario of attacks by a mouse with its own processing capabilities. The outcome of the work has proven that USB protocol remains open for exploitation. It highlights an important security risk because the attacks remain undetected by the latest operating system, security policies and anti-malware. The work further explained the components required and the procedural guideline to implement the attack to reproduce the outcome of the experiment and the capability of possible attacks that can be executed using the available command.
In conclusion, the work shown here brings attention to the deficiencies of USB in handling the authentication of devices connected to its end point. Therefore, Hardware Trojan Horse Devices can be customized with a variety of device classes to exploit these deficiencies.
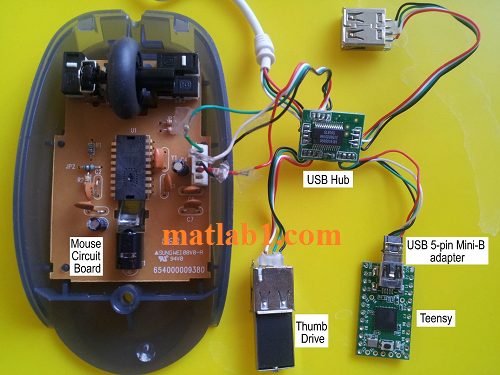
The components in the Programmable USB HID Mouse
This code has a document (59 pages) which describe the algorithm in detail.
REFERENCES
[1] B. Anderson, Seven deadliest USB attacks, Boston, MA: Syngress, 2010.
[2] D. o. H. S. Industrial Control Systems Cyber Emergency Response Team, “ICS-CERT Monthly Monitor,” October-December 2012. [Online]. Available: http://ics-cert.uscert. gov/pdf/ICS-CERT_Monthly_Monitor_Oct-Dec2012.pdf.
[3] L. Tung, “HP ships USB sticks with malware,” CNET, 9 April 2008. [Online]. Available: http://news.cnet.com/HP-ships-USB-sticks-with-malware/2100-7349_3- 6236976.html.
[4] S. Hargreaves, “How I ‘stole’ $14 million from a bank: A security tester’s tale,” CNN Money, 15 May 2013. [Online]. Available: http://money.cnn.com/2013/05/15/technology/security/bank-heist/index.html.
[5] D. Anderson, D. Dzatko and M. Inc, Universal Serial Bus System Architecture, Boston: Addison-Wesley, 2001.
[6] “USB Class Codes,” USB Implementers Forum, Inc, 7 December 2011. [Online]. Available: http://www.usb.org/developers/defined_class.
[7] D. V. Pham, Ali Syed and M. N. Halgamuge, “Universal serial bus based software attacks and protection solutions,” Digital Investigation 7, pp. 172-184, 2011.
[8] D. V. Pham, A. Syed, A. Mohammad and M. N. Halgamuge, “Threat Analysis of Portable Hack Tools from USB Storage Devices and Protection Solutions,” Victoria, Australia, 2010.
[9] D. Barrall and D. Dewey, “”Plug and Root”. the USB key to the Kingdom,” 27 July 2005. [Online]. Available: http://www.blackhat.com/presentations/bh-usa-05/BH_US_05- Barrall-Dewey.pdf.
[10] E. Levy and I. Arce, “Bad Peripherals,” IEEE Security & Privacy, p. 70, January/February 2005.
[11] J. Clark, S. Leblanc and S. Knight, “Hardware Trojan Horse Device based on Unintended USB Channels,” in IEEE Computer Society, Ontario, Canada, 2009.
[12] P. J. Stoffregen, “Teensy USB Development Board,” PJRC, [Online]. Available: http://www.pjrc.com/teensy/index.html.
[13] J. Clark, S. Leblanc and S. Knight, “Risks Associated with USB Hardware Trojan Devices used by Insiders,” in IEEE, Ontario, Canada, 2011.
[14] M. Fabian, “Endpoint Security: Managing USB-based Removable Devices with the Advent of Portable Applications,” in Information Security Curriculum Development Conference, Kennesaw, Georgia, 2007.
[15] A. Tetmeyer and H. Saiedian, “Security Threats and Mitigating Risk for USB Devices,” IEEE Technology and Society Magazine, pp. 44-49, Winter 2010.
[16] D. V. Pham, M. N. Halgamuge, A. Syed and P. Mendis, “Optimizing Windows Security Features to Block Malware and Hack Tools on USB Storage Devices,” in PIERS Proceedings, Cambridge, USA, 2010.
[17] M. Jodeit and M. Johns, “USB Device Drivers: A Stepping Stone into your Kernel,” in European Conference on Computer Network Defense, 2010.
Ardunio code for Mobile Robot Localization based on Kalman Filter by MCECS-bot
Ardunio code for estimation of orientation or attitude of a moving rigid body



Reviews
There are no reviews yet.