Mobile Ad Hoc Networks (MANETs)
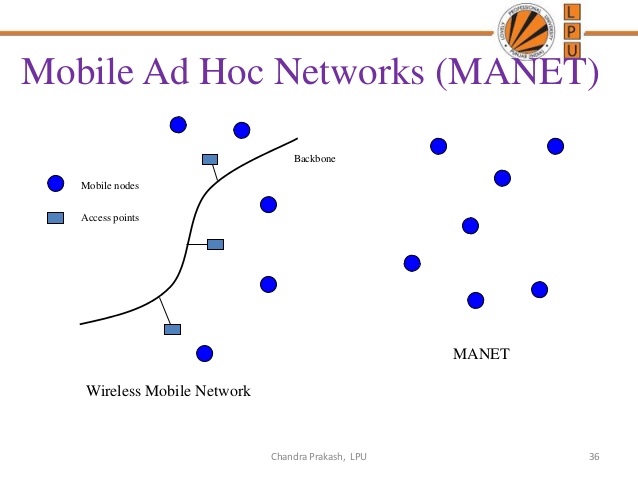
MANETs are made up of mobile devices that move in different directions at random speeds. These types of networks do not have any infrastructure and repeatedly configure themselves to connect with different devices in their communication range. MANETs are known for their dynamic behavior. Vehicular Ad Hoc Networks (VANETs), Smart Phone Ad Hoc Networks (SPANs), and Internet-Based Mobile Ad Hoc Networks (IMANETs) are different kinds of MANETs currently being used. As mobile devices move to different places, their resources and communication ranges vary.
Peer to Peer Communication
A group of networking devices that share information when interconnected to each other through a physical (cables) or a virtual (Bluetooth, Wi-Fi, infrared, and RF) medium is called peer to peer communication. In peer to peer architecture, every node has similar capabilities (such as communication range and storage space). Peer to peer communication is used for file sharing without a central server. Accessing the data from the neighboring nodes or replicating a file on other nodes can be marked as the best feature of peer to peer communication
Content Distribution in Normal MANETs
There are many protocols to access and send a file from one node to another node in their communication range. In a normal MANET, when a file is requested by the neighboring node, the query is satisfied by sending a replica of the requested file to the requesting node. When multiple nodes request the same file, the replica of the file is sent to all the requesting nodes. The request is sent as a broadcast by the requesting nodes, and the nodes that have the requested file will send the replica of the file to the requesting node, irrespective to other nodes. This causes redundancy and multiple copies of the same file in the requesting node. To avoid redundancy, every node periodically updates its list of files and arranges them according to their priority value. Furthermore, to effectively utilize the limited resources on every node, one or more groups of nodes maintain a list of files that are frequently requested. As specified in the book Handbook of Peer to Peer Networking, the replication protocols for normal MANETS can be listed below .· Static Access Frequency (SAF): In this file replication protocol, every node stores all the frequently queried files until the memory is full. As a result, duplicate replicas of the same file are formed among the neighboring nodes.· Dynamic Access Frequency and Neighborhood (DAFN): This protocol eliminates the formation of duplicate files among neighbors.· Dynamic Connectivity Based Grouping (DCG): The frequency of querying a file is called its priority value. In this protocol, duplication of the same file by neighboring nodes is eliminated, and the files are arranged in the descending order of their priority value.Node mobility disables the availability of the file that is replicated by both DAFN and DCG protocols. Managing the groups formed due to node mobility and avoiding the duplicates is the major challenge for the DCG protocol. As a result, traffic is high between the nodes following this protocol. Collecting the information from the neighboring nodes before replicating the file is a way to avoid the formation of duplicate files. K. Zheng et al. propose a protocol for addressing the file request . Every node should exchange the list of files before the replication of the requested file. The list of files is compared to check for the file availability and whether or not to replicate the file.
Content Sharing in Disconnected MANETs
As discussed in Chapter 1, disconnected MANETs have nodes that are randomly distributed among different areas. Y. Huang et al. propose a protocol to improve file availability in disconnected MANETs . The popularity of the file, node mobility, and Access Point (AP) topology are considered to optimize the file availability in a Wi-Fi environment. The corporativ caching method in disconnected MANETs helps store replicated files in a central node or server that are frequently visited by the nodes in that area. Due to node mobility, the central location of the node keeps varying constantly. To maintain the set of files at a central location, files are transferred from an old central node to a newly formed central node. This file transfer leads to
overhead.
Analyzing Optimal File Sharing in Peer to Peer Communication
The average number of time intervals needed to meet a file is calculated by in Equation (1)


 = probability of the node
= probability of the node  containing file
containing file ,
,
and the total number of nodes.
the total number of nodes.
The average number of time intervals required to satisfy the request is given by Equation (2)

Where,
 = Probability of requesting file
= Probability of requesting file 
and 
 Number of files in the network.
Number of files in the network.
The Random Waypoint Model (RWP) and the Community-Based Mobility Model (CBMM) are normal and disconnect MANETs respectively. For theoretical analysis, both node movement models are considered.
Theoretical Analysis of RWP for Normal MANETs
The Random Waypoint Model (RWP) contains nodes that move at random speeds. Theoretically, the probability of meeting different nodes is the same, but practically, this is not possible as nodes with greater speeds encounter more nodes. For optimal file replication, nodes follow exponential distribution to meet other nodes. Therefore, a previously encountered node does not determine the probability of meeting the next node. The average number of nodes a node meets in a unit time is referred as the meeting
ability  of that node. The probability of encountering the next node is node
of that node. The probability of encountering the next node is node  ,
,  , is given by Equation (3).
, is given by Equation (3).

Where,
 = Meeting ability of the node
= Meeting ability of the node  ,
,
and N = The total number of nodes.
 = Meeting ability of all nodes in the network (average meeting ability),
= Meeting ability of all nodes in the network (average meeting ability),
When vectors are assumed to contain file f, the probability of the next encountering node holding the file
are assumed to contain file f, the probability of the next encountering node holding the file is given by Equation (4). As
is given by Equation (4). As  considers the vectors, probability of encountering node I,
considers the vectors, probability of encountering node I,  , is equated to 1 and is replaced with
, is equated to 1 and is replaced with  .
.

Where,
 = probability of node ! holding file f,
= probability of node ! holding file f,
 = number of nodes holding file f and its replicas,
= number of nodes holding file f and its replicas,
and  = probability of
= probability of  node holding the file f or its replica.
node holding the file f or its replica.
In Equation (4), the resource allocated to the system (R) is given by the sum of the product of the storage space of node  and
and  , depicted in Equation (5).
, depicted in Equation (5).

Resources allocated to file f are given by , depicted in Equation (6).
, depicted in Equation (6).

 = size of file f.
= size of file f.
By multiplying and dividing with  and substituting Equation (6) in Equation (4),
and substituting Equation (6) in Equation (4),  can be expressed as Equation (7).
can be expressed as Equation (7).

The RWP mobility pattern follows binomial distribution to meet other nodes. The average number of time intervals required to meet the node with file f denoted by  is seen in Equation (8).
is seen in Equation (8).

Where,
 probability of meeting the file f after k time intervals.
probability of meeting the file f after k time intervals.
Therefore, the average time intervals to satisfy the request  is given by Equation (9).
is given by Equation (9).

According to Equation (9), the average query delay is dependent on  ,
, , and
, and  . As the values
. As the values  and
and  are predefined by the system, optimal resource allocation should be implemented to reduce the average query delay. Replace
are predefined by the system, optimal resource allocation should be implemented to reduce the average query delay. Replace  with
with  for simplification.
for simplification.

Therefore, the amount of resources allocated to the file f should be large to minimize  as seen
as seen
in Equation (10). To satisfy Equation (10), the resources allocated to file  should be equal to the resources of the network (R) as depicted in Equation (11).
should be equal to the resources of the network (R) as depicted in Equation (11).

Substituting the values of Equation (11) in the Equation (10), Min  can be written as Equation (12).
can be written as Equation (12).

To find the value of  , Equation (12) is differentiated with respect to
, Equation (12) is differentiated with respect to  and the resultant is equated to 0.
and the resultant is equated to 0.

By equating Equation (13) and Equation (14), Equation (15) is achieved.

When the second order derivative is applied to Equation (12), the value should be greater than 0 to achieve minimum query delay.

Equation (15) satisfies the maximum resource allocation condition, Equations (16) and (17) can also be represented as Equation (18) and Equation (19).


If resource allocated to the file f is greater than the resource allocated to the rest of the
files ![R_f\gt R_F(R_f\in [1,F-1])](https://matlab1.com/wp-content/plugins/wp-fastest-cache-premium/pro/images/blank.gif) , Equations (18) and (19) are satisfied. If the value of the resource for
, Equations (18) and (19) are satisfied. If the value of the resource for
the  file is substituted in place of
file is substituted in place of  , the equations holds well only if
, the equations holds well only if ![R_f\gt R_k(f\in [1,F],f\notin k)](https://matlab1.com/wp-content/plugins/wp-fastest-cache-premium/pro/images/blank.gif)
So, it is concluded that if the first condition is true, then the second condition is automatically satisfied. This happens only because there is always a file that has lesser resources allocated to it. Therefore, the resource allocated to the file f can be written as

From Equation (20), it is acknowledged that the resource allocated to the file f is directly proportional to the square root of 

Since  =
=  , the value of
, the value of  is replaced by
is replaced by in Equation (21).
in Equation (21).

From Equation (22), the sum of meeting abilities of all the nodes holding file f is proportional to priority value  . This condition should be satisfied to achieve a minimum query delay.
. This condition should be satisfied to achieve a minimum query delay.