Artificially Intelligent Industrial Contorollers
The purpose of this research was to propose increased role for Artificial Intelligence (AI) for adaptive measures in cybersecurity for Industrial Controllers (IC) to provide Resilient Control Systems (RCS) and improve cybersecurity for such devices. Control of and access to critical industrial controllers requires updated security. AI may prove valuable by increasing resiliency and reducing the vulnerabilities to such systems. The proposed research improves upon the defense-in-depth strategy with an added layer to mitigate current security vulnerabilities. Key questions include: What indicates a need for advanced security in industrial controllers in current systems? How can AI mitigate vulnerabilities and threat levels to Industrial Control Systems (ICS) and critical infrastructure? How will AI improve IC to introduce RCS? Malicious computer code, first identified in 2010, targets IC’s. Stuxnet’s ability is a model of “malware” capable of infiltration and destruction of specific process control hardware. Code designed as a warfare tactic and executed by a nation-state lead to the term “cyberweapon.” A succinct description of cyber weapon are cyber means a conflict intended to cause injury or death of people or damage to, or destruction of objects. A substantial issue is increasing terrorist events and malevolent code targeting Critical Infrastructure and Key Resources (CIKR). Attacks designed to damage or disrupt infrastructure target ICS.
nformation Assurance
CIKR no longer preserves boundaries that restrict infiltration from external networking. Businesses now link CIKR to the Internet, compromising the ideal state for an Industrial Control Network (ICN) . Interlocking these networks with the Internet necessitates that mainstream Information Technology (IT) adopt defense-in-depth protocols. Involving patch management, network segmentation, authentication, application control, event management, and intrusion management is an expectation in these systems . All are facets of the technology division of Information Assurance (IA). IA conjoins hardware and software with people, operations, and technology . ICS’s are not atypical IT environments . Security postures associated with ICS’s require better defensive metrics because they are involved in multi-tier frameworks. Their components can interface with enterprise networks . Available connections between enterprise and remote field locations validate IC security concerns. Figure 1 provides an example of the IA framework.
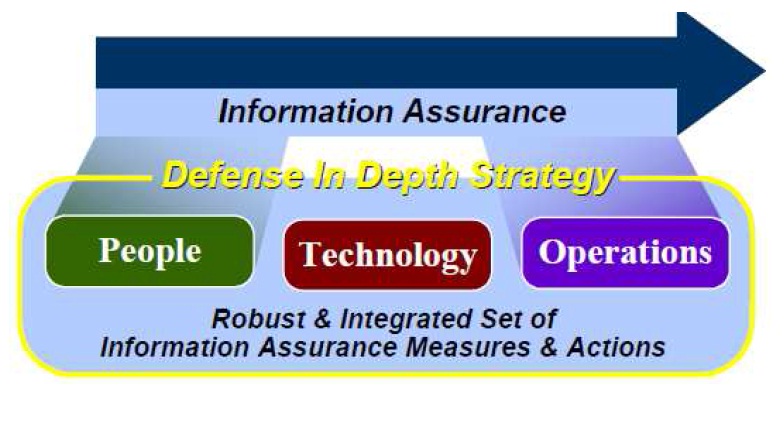
Figure 1. IA defense in depth strategy by Defense in Depth.
Organizations should; 1) expect attacks on these systems, 2) have tools to detect intrusion, and 3) procedures for incident response and recovery. A troubling feature of IC’s is their physical link. This physical state connects to the virtual state presenting a keystone of ICS security. The entire façade is at risk of collapse without proper networking, operational procedure, and element segmentation .