Operational Impact
An operational impact of a cyber-attack is measured the same as maintenance, power outage, or any other cause when the system becomes unusable or unavailable. Cyber-attacks are complex and dynamic in nature. Attacks, once successful, allow hackers go to work. Hackers conducted attacks similar in nature on Sony, the FAA, Air Canada, Ctrip.com, American Airlines, Polish Airlines, and Britain Civil Aviation. If not corrected, the vulnerabilities seen in Automated Dependent Surveillance-Broadcast (ADS-B), a system used by airlines to communicate their location to air traffic control towers, will join the growing list of systems attacked.
Sony
In 2014, Sony reported that hackers had taken down the Sony PlayStation Network; however, reported no compromising of user data. Sony’s PlayStation Network was down approximately a week and caused game players outcry (Express Computer, 2014). Sophie Knight and Malathi Nayak, journalists for Reuters, reported that authorities diverted American Airlines flight 362, which was traveling from Dallas to San Diego, due to a bomb scare in which a top Sony executive was traveling (2014). The FBI investigated the bomb threat that coincided with the Sony hack and further coincided with the bomb scare (2014). Diversions of this kind cause high anxiety for all passengers, not to mention the cost to the airline for rebooking passengers who may have missed connecting flights (Knight & Nayak, 2014).
FAA
Aliya Sternstein, senior correspondent for NextGov, authored articles on cybersecurity and homeland security systems. In 2015, Sternstein reported the FAA experienced an attack when hackers deployed malicious software on the FAA’s computer system. The virus, spread by email, was only affecting administrative computers. The FAA raised concerns that virus vulnerabilities leave the system at risk for cyber-attacks and their effects on the air traffic control systems could be substantial (Sternstein, 2015).
Air Canada
In 2003, the Welchia worm attacked Air Canada’s systems rendering the airline’s ability to process passengers at reservations centers and call centers. The Welchia
worm, designed to remove the ‘Blaster’ worm by downloading updates directly from Microsoft, did the opposite. The Welchia worm locked out administrators preventing them from removing the ‘Blaster’ worm and updating computers. Air Canada’s experience caused delays and numerous cancelations of flights (Airline Industry Information, 2003).
ADS-B
Andy Greenberg covers data security, privacy, and hacker culture for Forbes. In 2012, Greenberg reported that a new system known as ADS-B was set to be in place by 2020. ADS-B shifts how aircraft communicate their location to air traffic control towers. Today, airplane communications depend on towers for radars to track and coordinate their locations. The new system, ADS-B, moves the communication to regular radio frequency and is an as easier, cheaper, and safer means of communication (Greenberg, 2012). The FAA completed the deployment of 634 ADS-B to ground stations in 2014. According to the FAA, 6,000 general aviation aircraft and 225 commercial aircraft have been equipped with ADS-B Instrumentation (FAA, 2015). Figure 4 shows Surveillance and Broadcast service as of February 2015.
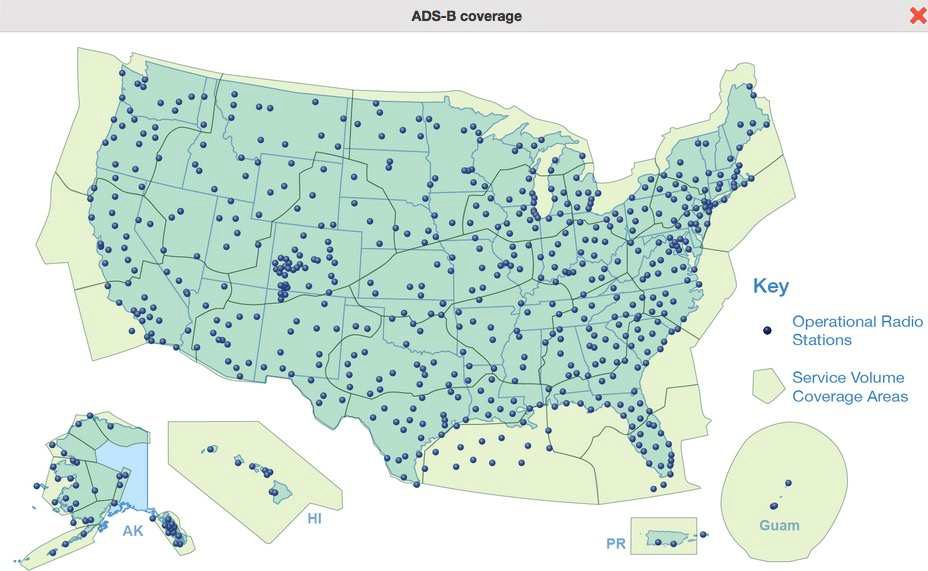
Figure 4. Installed ADS-B at 634 ground stations (FAA, 2015, ADS-B Today, para. 6).
Deployment of new technology such as the FAA’s Next Generation Transportation Systems (NextGen aircraft tracking, will need to be able to withstand a cyber-attack. NextGen will also need to perform with minimal to no vulnerabilities to its systems. NextGen’s use of ADS-B technology has prompted criticism that its design architecture is not secure enough and will be vulnerable to cyber-attacks. Network security consultant and hacker, Brad Haines (also known as RenderMan), is concerned that ADS-B does have vulnerabilities. Since transmission occurs over radio waves at 1090 MHz for commercial aviation and 978 MHz for general aviation, injecting flights into the system is possible. Injection attacks are just one example, others include eavesdropping, man in the middle, and denial of service (Haines, 2012).
Polish Airlines
Eric Auchard and Wiktor Szary, journalists for Reuters, reported in 2015 that Polish Airlines experienced a cyber-attack causing their systems to become inoperable. A DDoS attack disabled the Polish Airlines system used for issuing flight plans, which subsequently caused 1,400 passengers stranded at Warsaw’s Chopin airport. The flight plan system was down for about five hours, not only stranding passengers, but also grounding planes (Auchard & Szary, 2015).
Ctrip.com International
A cyber-attack forced China’s biggest travel agency offline for 12 hours. The customers who attempted to reach Ctrip.com via the website or mobile application reached a page displaying service unavailable. Technicians for Ctrip.com worked to restore servers damaged by the attackers (AsiaOne, 2015).
American Airlines
Brigham A. McCown is a contributor for Forbes. In his article titled, “American Airlines Grounded. Accident or Potential Cyberattack?” McCown (2013) reported that in April 2013, American Airlines experienced an outage with their computer system. The outage caused delays and cancelations of about 2,000 of their daily flights. The cause of the outage was unknown. However, reports attributed the outage to a communication issue between American Airlines and their central reservation system run by Sabre Holdings. Airlines are dealing with attacks which impact a large number of their flights throughout their systems may not only face the challenge of restoring its systems, but also the snowball effect caused by cancellations and delays. The disruption continues by creating a cascading effect that may take days, if not weeks, to resolve. Further, the disruption affects the airline’s long-term bottom line as they deal with the aftermath of a cyber-attack.
Britain Civil Aviation
David Morgan a reporter for ABC News reported on a hijacking of communication radio transmission to airplanes usually transmitted by the air traffic control. Britain’s civil aviation issued a safety alert after air traffic controllers overheard the pilot’s communication to and from unknown sources providing the pilots with false instructions. The hackers used a portable transmitter to communicate with the pilot. Investigations point to the hackers using a transmitter, which cost $450 and which requires a license to operate legally (Morgan, 2011). According to Morgan, Richard Dawson, president of U.K.’s Guild of Air Traffic Controller stated, “This is a criminal act which could ultimately result in a serious accident. The problem is that the people making these spurious calls are mobile and can be very difficult to trace” (Morgan, 2013, Hackers Attack Air Traffic, para. 6).
Potential Revenue Loss
Susan Berfield, a writer for Bloomberg Business Week, reported in 2014 that the breach experienced by Target greatly affected company revenue during the crucial holiday shopping season. Target was a perfect example of the significant impact a cyber-attack had on its business and the revenue loss resulting from the attack. Revenue is the most important area for any company providing services or goods. A cyber-attack cannot only affect revenue, but future standings of the company. The cyber-attack on Target led to net profits dropping 46%, costing $61 million, and over 80 civil lawsuits. Companies are under increased pressure to raise profits more than applying security measures to the organization (Berfield, 2014). Similarly, Sony Pictures saw a revenue impact on a second cyber-attack in 2014. Tim Hornyak, an IT reporter on telecommunications, science, and technology reported that $35 million was the cost estimate from Sony’s 2014 cyber-attack. Included in the figure is $15 million to repair damaged equipment, investigation, and remediation (Hornyak, 2015). Aeroflot Airlines is another example that shows the impact on revenue due to a cyberattack. The cyber-attack, driven by the DDoS attack and lasting several days denying access to ticket sales, came with a hefty price. Assist, Aeroflot’s processing company, lost $488,090 in revenue. Aeroflot, felt a great impact as a result of the cyber-attack, reported a loss of more than $4.75 million in revenue (Russian Legal Information Agency, 2013).
Chris Harris, a freelance journalist, has authored numerous publications in Information anagement and Enterprise for InformationWeek. In 2011, Harris reported that in one year, small enterprises lost an average of $55,000, midsize enterprise lost an average of $91,000 or more, and large enterprises had losses exceeding $1,000,000. The figures explained are only for IT outages and are not part of a cyber-attack. However, adding a cyber-attack event to the figures, the figures can triple, costing millions of dollars in loss to the enterprise (Harris, 2011). Airlines Reporting Corporation (ARC), which settles all transactions between airlines and United States travel sellers, noted an increase in fraud in 2011. ARC reported an increase in unauthorized, fraudulent charges of airline tickets with a face value of all tickets issued at one million dollars, with one single instance at over $77,000. The fraudulent charges according to ARC were from phishing emails aimed at travel agents and independent contractors. Travel agencies received an email that appeared to the travel agents as if the message came from Global Distribution Systems (GDS). The email directed the agents to a website to make bookings on which hackers track personal information (Dark Reading, 2011).
Similarly, China’s largest travel agency Ctrip.com encountered a cyber-attack that cost Ctrip.com a loss of $1.44 million per hour. The outage experienced by Ctrip.com cost a total of $16.8 million excluding the cost of hardware replacement. The attack coincidently occurred after Ctrip.com received $250 million subsidies from Priceline.com LLC (AsiaOne, 2015). The deployment of the FAA’s NextGen ADS-B also comes at a cost due to increased implementation costs. The initial systems came with benefits, however; it currently is of little use to commercial airlines at this time. The cost of NextGen has outweighed the benefits. NextGen has increased cost for both FAA and airspace users by $588 million (Targeted News Service, 2014). Brianna Ehley, a journalist at The Fiscal Times reported in 2014 that the estimate of NextGen’s $4.5 billion cost though 2035 is about $400 million more than the original cost. The Inspector General warns the cost could even go higher (Ehley, 2014). The FAA’s number of underlying programmatic reforms associated with NextGen hinders the implementation of new capabilities to realize all full benefits. The cost of NextGen will eventually affect commercial airlines when systems in the aircraft need replacement (Targeted News Service, 2014).
Bruce Schneider, a chief technology officer at Resilient Systems, published in 2015 that newer generation planes such as Airbus A350, A380, and the Boeing 787 Dreamliner have one network. The network contains both, the plane’s internal network and passenger wireless Internet (Wi-Fi) connections. Mixing the aircraft computer systems network with the passenger cabin Internet connection could allow a terrorist the means to have multiple planes to collide. The terrorist could be sitting at the back of the plane or on the ground working on taking control of the plane (Schneier, 2015).
Additional revenue impacts may include the protection airlines pay for victims of a data breach. US Airways provided their pilots who were part to the data leak exposure with 12 months of life LifeLock (Higgins, 2011). LifeLock provides consumers with identity protection costing in the range of $9.99 to $29.99 a month depending on the services (LifeLock, 2015).

