Encryption Software On Mobile Devices
Encryption Software On Mobile Devices
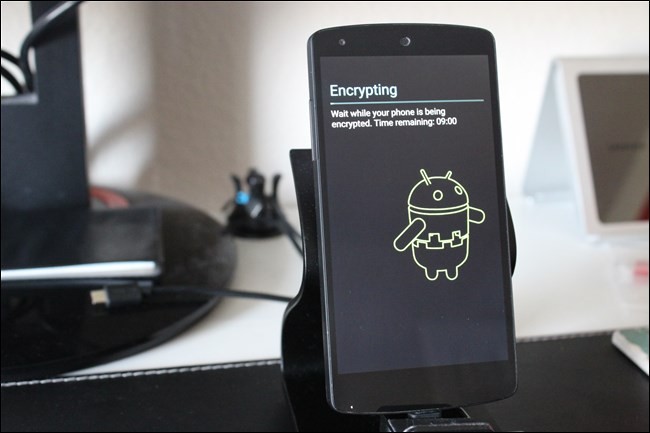
According to Peroni (2014), end users have the
options to apply encryption algorithms on their iPhones and Android-based smartphones since these devices are preconfigured with built-in encryption capabilities (setting passcodes on iPhones and passwords/PINs on Android-based smartphones), albeit not turned on by default (para.5). At the time of writing this research paper, “Currently the Windows Phone does not support encryption” (Peroni, 2014, para. 5). These form of device encryption are considered FDE (Full-disk Encryption) primarily due to the nature of its encryption capabilities for iPhones and Android-based smartphone devices. “It is extremely difficult for hackers to enter, but it is also difficult for users to enter. Logging into the device takes longer when encryption is enabled” Peroni, 2014, para. 6).
Since the aforementioned pertains to manufacture-enabled encryption options for the physical device, which may not be an ideal or practical option to satisfy all end users of mobile devices, in particularly—mobile phones. There are alternative encryption solutions that end users can opt to use, which are encryption software and/or apps developed by third-party vendors to meet mobile consumer demands. Peroni (2014) also mentioned “In addition to data encryption, voice encryption is also available. Voice encryption scrambles vocals between the end-to-end communications, preventing interception” (para. 8).
As for the encryption software availabilities, the options available will depend on the versions of operating system platform running on the mobile device (i.e., Android, iOS, and Windows). UW Medicine Information Technology Services (2012), recommended two popular mobile encryption applications for Android-based devices: Encrypt It and Droid Crypt. The encryption software options for Android-based mobile devices is still a new phenomenon.
Software available is still limited for mobile device users. As for iOS-based mobile devices, encryption software or apps are nearly non-existent, primarily due to the built-in FDE encryption capability feature from Apple, Inc.
Although in recent years, consumer demands for increased security via data and/or device encryption functions have put stress tests on mobile device manufacturers (e.g., Google, and Apple) to integrate innovative encryption solutions, to include partnership with third-party vendors to enhance mobile security, mobile data encryption is still a new concept, and requires further research and development to expand the software and/or app availability for crossplatform mobile devices. At the time of writing this research paper and based on the information available, the author discovered there are limited software-based mobile encryption options available for consumers who are looking to incorporate additional data encryption solutions that are freely available on mobile devices for file-based, folder-based, and/or FDE capabilities to enhance data protection.
Level of encryption required for the end user
In regards to this topic, the level of encryption that the mobile device end user needs, ultimately depends on the type of data,
information, and/or communications content stored or available on the device in question.
Additionally, According to SANS Institute (2011), “One of the best ways to protect data on a mobile device is to encrypt it” (p. 1). Encrypting the contents such as files, folders, and/or the mobile device itself will further prevent and/or deter unauthorized users from viewing the contents on the mobile device. On the one hand, data encryption of any level will play an important role in secure the information stored on the mobile device—creating an extra layer of data security protection to ensure confidentiality, integrity, and availability (CIA) of the stored information and/or data on the mobile device. Especially, when the mobile device is misplaced, loss, or stolen. Mobile users will have to make the determination on the level of data encryption that is required. On the other hand, “While encryption offers another layer of protection, it also creates a barrier that goes both ways” (Peroni, 2014, para. 6). This protection barrier makes it difficult for the average hacker, but is not to be taken as bulletproof. Schneier (2008) also confirmed “There’s no such thing as absolute security, and any gain in security always involves some sort of trade-off” (p. 51).
According to Peroni (2014), “Some of the more sophisticated hackers have successfully breached smart phones” (para. 9). Encrypting one’s mobile device using available encryption options (e.g., third-party software-based or device-based on iPhones and Android devices) only adds a layer of protection to the overall security of the device. It is recommended that end users of such devices install additional parameter defense applications (e.g., firewalls, antivirus applications, and security patch updates), and configure strong passcodes and/or passwords/PINs to strengthen the level of security to protect the sensitive data that resides on the mobile device in question. Furthermore, it is worth noting that the level of encryption that mobile device end users consider will also need to ensure that the password, passcode, and/or PIN that is used to encrypt the data (i.e., file, folder, and device, also known as FDE) is configured as a strong selection.
According to SANS Institute (2011), “encryption is only as strong as the security of your computer. If your computer is infected, the bad guys can compromise your encryption” (p. 2). When it comes to deciding what level of encryption and/or whether to even consider what type of encryption or available encryption methods are available on the types of mobile devices can be a daunting task. End users are often unaware of the types of available encryption software for the intended mobile devices (i.e., Android-based, Windows-based, and iPhones). To add to the frustration, end users frequently are ignorant or uneducated as to whether the stored information and/or data on the mobile device in question requires any form of encryption at all.
UW Medicine Information Technology Services (2012) provided a simple solution by introducing the following flowchart to assist end users in determining the need for data encryption, as shown in Figure 5.

Figure 5: Mobile Device Data Encryption Flow Chart
Source:
https://security.uwmedicine.org/guidance/technical/encryption/MobileDevice_Encryption/ChooseEncryptionFlowChart.pdf
